CMS Version
Docker 2.3.4
Player Type
Windows
Player Version
R202 White Labled
Issue
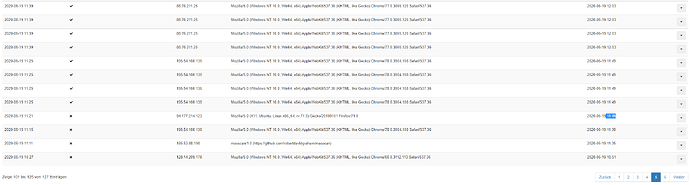
We have two Servers. In both I have (unknown) IPs under Session without a username attached. It seams that they are all over the globe. On one server there are only a few without a username (10 as I start writing, 0 right now as I would take a screenshot?), all marked as active (in spite there session runs out some time/days ago). On the other, an azure cloud server, there are a couple per hour to 100 per minute, and there they are not marked as active when the session runs out some times ago.
All this leads to this questions:
-
Does “no username” means that this are login attempts without success!? Or eg. just port scans? Or are there really attacker logins with an empty-string username (maybe exploits a security-bug)? With other words, should we be worried and what can/should we do about it (how can we investigate further)?
-
How is it possible that a session is active while it runs out long time ago? Or does this things doesn’t mean what it looks like? And if that’s the case, what does that all means?
I know, there is an old question with the same case, but non of the important questions gets answered there.
So I hope you can bring light to these events.
I think, for authorized users, it should always looks like this: